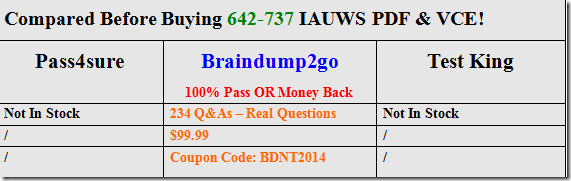
[2016 Feb-Latest]New Released Braindumps:2016 Braindump2go Cisco 642-737 IAUWS Dumps Instant Free Download
2016 February NEW 642-737 IAUWS PDF & 642-737 IAUWS VCE RELEASED Today!
Exam Code: 642-737
Exam Name: Implementing Advanced Cisco Unified Wireless Security (IAUWS)
Certification Provider: Cisco
Corresponding Certification: CCNP Wireless
Test Time: 90 minutes (50-60 questions)
2016 NEW 642-737 IAUWS Study Guide:
1. Integrate Client Device Security
2. Design and Integrate Wireless Network with NAC
3. Implement Secure Wireless Connectivity Services
4. Design and Implement Guest Access Services
5. Translate Organizational and Regulatory Security Policies and Enforce Security Compliance
6. Configure Native WLC Security Feature Sets: IPS/IDS
7. Integrate Wireless Network with Advanced Security Platforms
ATTENTION: If you want to pass the 642-737 IAUWS Exam, those 2016 NEW ADDED 642-737 IAUWS Questions are the most IMPORTANT!
QUESTION 194
What device will authenticate the user when a sponsor creates a guest account on the Cisco NGS?
A. WLAN controller
B. Cisco ACS
C. Cisco NGS
D. active directory server
Answer: C
QUESTION 195
A lobby ambassador is creating guest access accounts. At which two locations can the accounts be stored? (Choose two.)
A. NAC guest server
B. Active directory
C. WLAN controller
D. WCS
E. ACS
Answer: CD
QUESTION 196
An engineer is configuring the guest WLAN to redirect to a created login page uploaded to the controller. Which three CLI commands are required if the guest WLAN is on WLAN 2? (Choose three.)
A. config wlan security web-auth enable 2
B. config wlan custom-web global enable 2
C. config wlan custom-web webauth-type customized 2
D. config wlan custom-web login-page login.html 2
E. config wlan custom-web webauth-type internal 2
F. config wlan custom-web login-page customized 2
Answer: ACD
QUESTION 197
An engineer creating a configuration file to upload to a controller would like the guest WLAN to be set for L3 authentication only. What command must be included in the configuration file?
A. config wlan security web-auth enable 2
B. config wlan security wpa wpa2 disable 2
C. config wlan security web-auth server-precedence 2 local radius ldap
D. config wlan custom-web global enable 2
Answer: A
QUESTION 198
An engineer is configuring the anchor controller for a guest network. What setting in the guest WLAN can be different from the foreign controllers?
A. VLAN
B. radio policy
C. QOS setting
D. WLAN advanced settings
Answer: A
QUESTION 199
All users on one of the two guest WLANs are failing to connect after a configuration change was made to a controller. What is the cause of the outage?
A. The interface or VLAN of the anchor controller and foreign controller no longer match.
B. The configuration of the failing WLAN no longer matches the foreign controllers.
C. The address of the NAC guest server has been changed.
D. The DHCP server on the foreign controller was changed.
Answer: B
QUESTION 200
What three items can be found on the Wireless Control System PCI DSS Compliance Report? (Choose three.)
A. all authentication and encryption violations
B. all ACL violations and reports
C. all IDS threats
D. detailed association history for clients connected to the network
E. all SSIDs not using Client Exclusion
F. all access points that have rogue detection enabled
Answer: ACD
QUESTION 201
An engineer is segmenting WLAN traffic by security options after the client has received an IP address. Which two security options are possible? (Choose two.)
A. web policy
B. Cisco Key Integrity Protocol
C. PSK
D. 802.1x
E. VPN pass-through
Answer: AE
QUESTION 202
An engineer is configuring 802.1x authentication on an autonomous AP. What two configuration commands must be included on the AP if the RADIUS server IP is 10.9.4.9? (Choose two.)
A. radius-server host 10.9.4.9 auth-port 1812 acct-port 1813 key Cisco123
B. aaa new-model
C. aaa authorization
D. aaa attribute list 10.9.4.9
E. aaa group server radius 10.9.4.9
Answer: AB
QUESTION 203
An engineer has configured passive fallback mode for RADIUS with default timer settings. What will occur when the primary RADIUS fails then recovers?
A. RADIUS requests will be sent to the secondary RADIUS server until the secondary fails to respond.
B. The controller will immediately revert back after it receives a RADIUS probe from the primary server.
C. After the inactive time expires the controller will send RADIUS to the primary.
D. Once RADIUS probe messages determine the primary controller is active the controller will revert back to the primary RADIUS.
Answer: C
QUESTION 204
What is the default SYSLOG level in a wireless LAN controller?
A. alert
B. notification
C. error
D. informational
E. debugging
Answer: C
QUESTION 205
An engineer is configuring IDS signatures and sets Bcast deauth to enabled and immediately begins to see Broadcast deauthentication frame alerts.
What Cisco recommended solution would resolve this issue?
A. disable Bcast deauth
B. disable Broadcast SSID on the WLAN
C. enable MFP on the WLAN
D. locate and disable the attacker
Answer: C
QUESTION 206
Client adapters on the wireless network are locking up and a packet capture shows many management frames with no SSID element.
What signature should the engineer enable for the WLC to report this issue in the future?
A. Deauth flood
B. Null probe resp 2
C. EAPOL flood
D. Wellenreiter
Answer: B
QUESTION 207
The controller is reporting an IDS signature ‘deauth flood’ attack and it has been determined that the default settings are too sensitive for the environment.
What signature details should be adjusted to only trigger the alert on a certain amount of client packets within a certain period of time?
A. Measurement Interval and Quiet Time
B. Signature Frequency and Signature MAC Frequency
C. Measurement Interval and Signature MAC Frequency
D. Quiet Time and Signature Frequency
Answer: C
QUESTION 208
When creating a custom rogue classification, what three conditions would be added to alert on a specific internal SSID with more than 5 clients at -80db? (Choose three.)
A. SSID
B. RSSI
C. SNR
D. duration
E. client-count
F. managed-ssid
Answer: BEF
QUESTION 209
Many users report being disconnected from the WLAN and WCS shows events for broadcast deauthentication frames. What security feature mitigates the issue?
A. WPA2
B. MFP
C. IDS
D. ACL
E. IPS
Answer: B
2016 February NEW 642-737 IAUWS PDF & 642-737 IAUWS VCE Full Version:http://www.braindump2go.com/642-737.html